Mobile phones have integrated as an essential element in our day-to-day life. Presently, along with swift communication, it is tremendously used for Payment of Bills, E-commerce Shopping, Health Monitoring, GPS Navigation and more. A similar progressive trend is observed with access control, which initiated with RFID Cards, then expanded with biometrics and now it is being enhanced with advanced mobile credentials like Bluetooth.
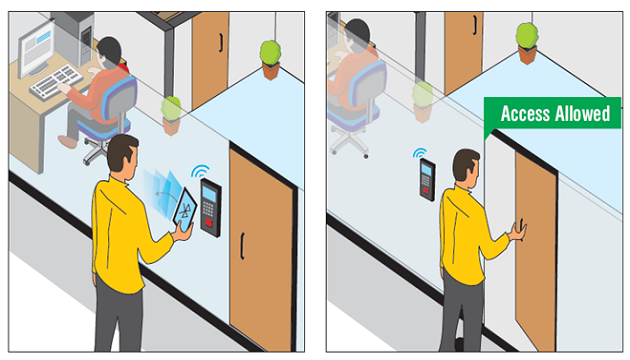
Matrix offers gesture-based identification of users. It’s “Your Mobile is your Identity” allow users to mark attendance and gain access by simply twisting their mobiles in the vicinity of the entry or exit point. Matrix has evolved the mobile technology whereby basic Access Control and Time-Attendance functions can be carried out on a mobile. Bluetooth based Access Control allows access to users just by a gesture of a phone in front of the device.
Benefits:
• Simply twist your mobile phone in the vicinity of the device to gain access and mark attendance easily.
• Works where biometric devices are difficult to access.
• No constraint on a number of users compared to biometrics.
• Works on Mobile’s Unique IMEI Number
• Wireless and No Physical Contact with Sensor
• Requires One-Time Bluetooth Pairing
• Secured Communication between Server and Mobile
Solutions:
Twist Mobile and Get Access
Gesture-based “Your Mobile is your Identity” technology provides automated wireless access control, which allows users to open a door from a distance by simply rotating their smartphones. As a result, multiple users can simultaneously gain quick access.
Reliable and Secured Communication
Matrix ensures secured communication between device and server, as the data exchanged between them is encrypted. Only the registered mobile phones can have access. Moreover, Bluetooth-based Access Control diminishes False Acceptance Ratio (FAR) and False Rejection Ratio (FRR). It provides convenience to install a device, irrespective of the location. There is no need to enter a password on the touch screen and there are no additional devices needed.
• Contact: MATRIX COMSEC
394 GIDC, Makarpura, Vadodara
+91 93744 74302
More@MatrixComSec.com